Crowdsec Installation on rpi3 with DietPi / Raspberry OS
Today, we are going to see how to install Crowdsec on a Raspberry Pi 3 with DietPI . It works with Raspberry OS (Raspbian) too.
As a reminder, DietPi is a lightweight and optimized OS (RAM, CPU, reduces SDcard writes, etc). Crowdsec is an open source and free system which parse system and applications logs inorder to build a bad IP qui permet de constituer a community database of malicious IPs. We can block IP with a firewall (iptables, Nftables) or at web server level (nginx for example).
Crowdsec Installation
Once DietPi installed and updated (see the official site here), you have to install golang because default crowdsec binaries don’t run on ARM platforms, so we have to build it. The minimum version of golang supported is 1.13, so we cannot use the repository’s packet (1.11). We need to install manually from golang.org.
wget https://golang.org/dl/go1.15.6.linux-armv6l.tar.gz
sudo tar -C /usr/local -xzf go1.15.6.linux-armv6l.tar.gz
Now we are going to modify the profil to set the paths to go’s installation.
nano ~./profile
#on ajoute les 2 lignes ci-dessous
PATH=$PATH:/usr/local/go/bin
GOPATH=$HOME/go
#on recharge le profil
. .profile
Then we install the prerequisites and download Crowdsec’s sources (v1.0.2 when I wrote this post) :
sudo apt-get install bash gettext whiptail curl wget
git clone https://github.com/crowdsecurity/crowdsec.git
tar xzvf crowdsec-release.tgz
cd crowdsec-v1.0.2
export GOARCH=arm
export CGO=1
nano MakeFile
We edit the Makefile to modify the variable GOARCH to “arm” :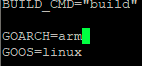
Then we install the compilator gcc-arm-linux-gnueabihf
sudo apt install install build-essential gcc-arm-linux-gnueabihf
And we build with make, then we can run the wizard :
sudo ./wizard.sh -i
If the list of services is empty, it means you let the default ssh system in DietPi (DropBear) which is not detected by Crowdsec. You have to launch Dietpi-software ,install openssh and remove dropBear.
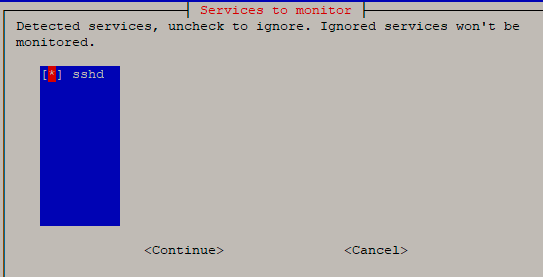
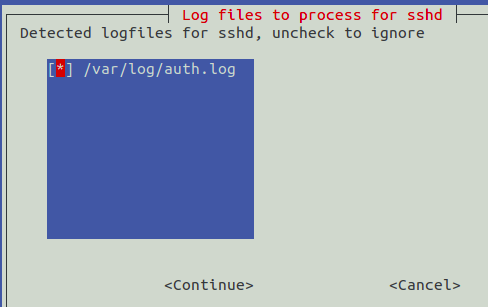
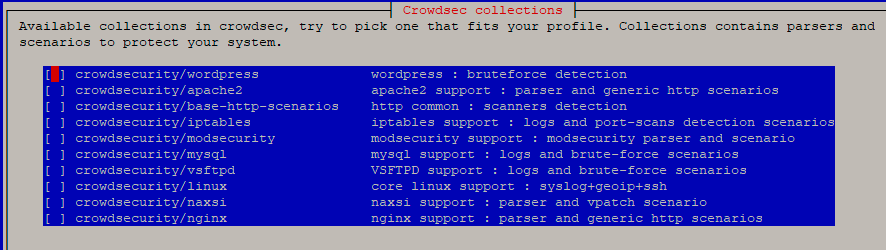
You can let the default configuration for ssh. Otherwise adapt according to the services installed (http, smtp, etc).
Now we can use the commandcscli which allows to interact et manager Crowdsec (delete/addscénarios, bouncers, api, etc). You can use the command cscli help to know the commands list.
Examples of use :
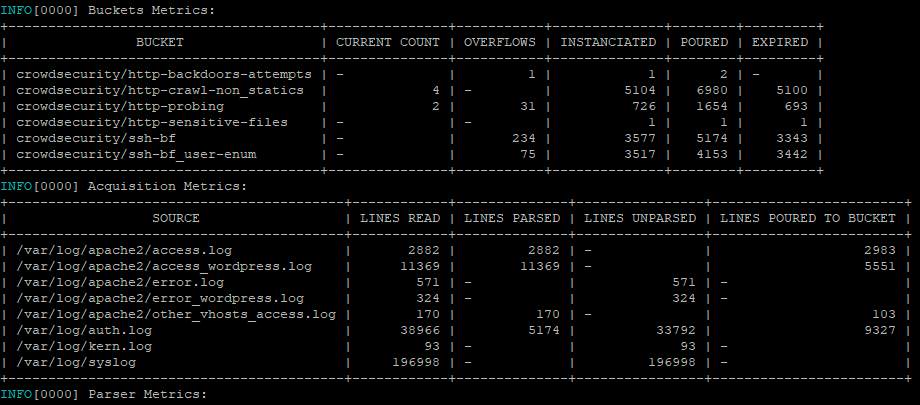
cscli metrics (displays statistics) :
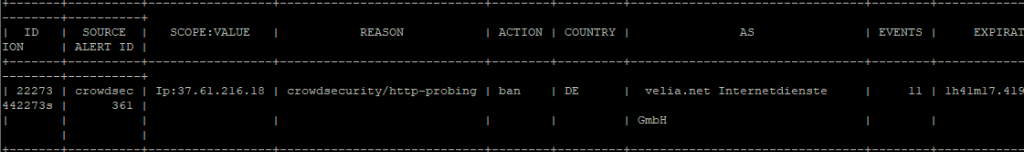
sudo cscli alerts list (display alerts) :
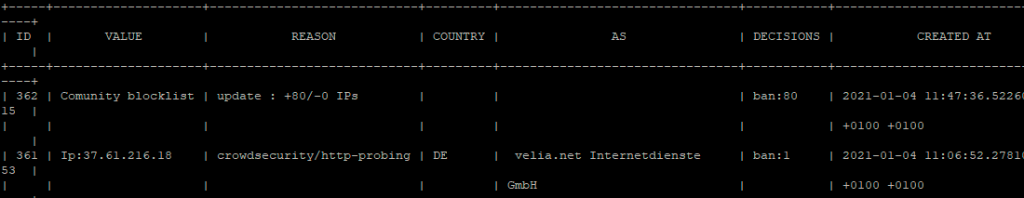
sudo cscli decisions / cscli decisions delete -i 1.2.3.4 / cscli decisions add –range 1.2.3.0/24 (show decisions, add it or delete it) :
All the configuration’s files are stored in /etc/crowdsec and the log files in var/log/crowdsec*.
We have seen the installation of Crowdsec which allows analyse of logs and feed the malicious IPs database and take decisions but no IPs will be blocked because it is necessary to install a bouncer which query the database (via the api) and block the connection according to its configuration(firewall, nginx, etc). Go to Crowdsec Nginx Bouncer .
Leave a Reply